The Best Phone Tracker for Parental Control by Employee
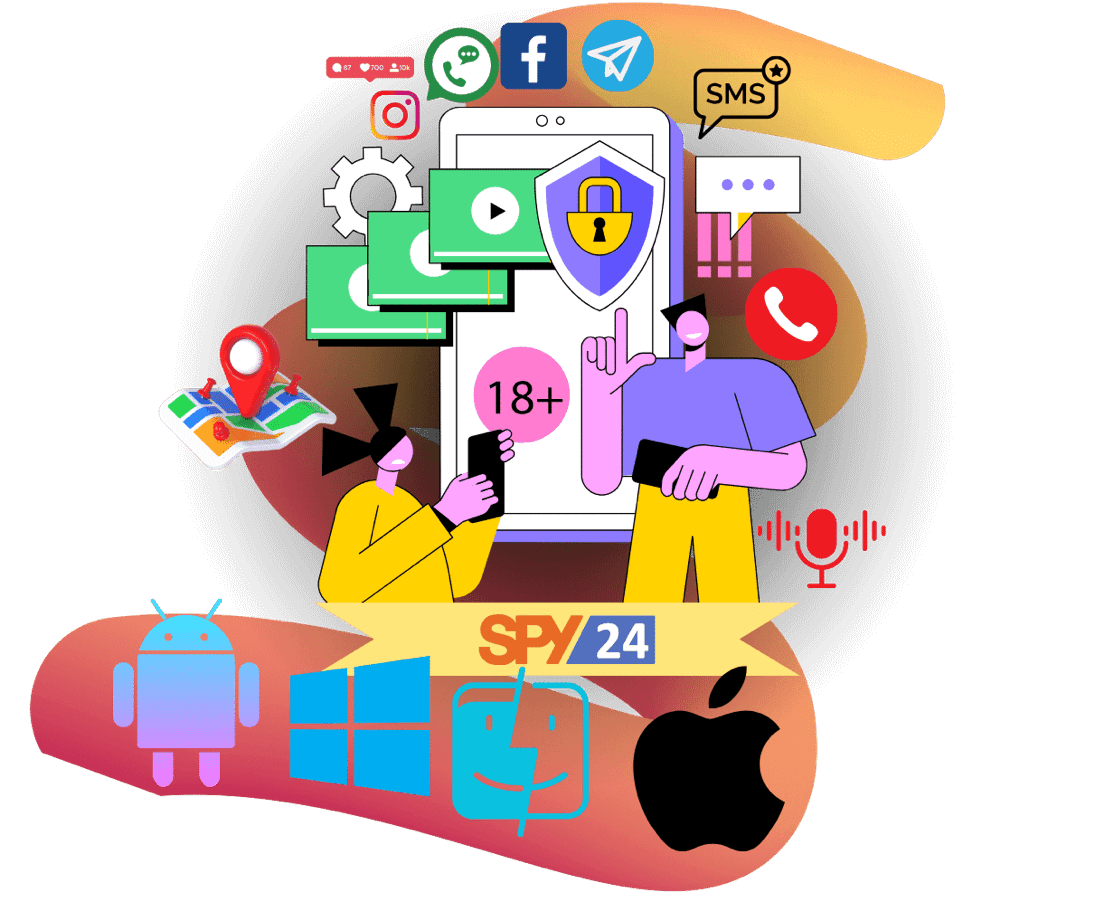
Start tracking all activities right now with the most efficient monitoring solution that is truly perfect for parental control and employee time tracking when you have multiple employees or some of them work remotely. Gain decisive data and monitor everything that happens in real time for peace of mind. Use the SPY24 monitoring app on Android, iOS, Windows, and macOS devices right now!
- + Track all calls and texts, including the deleted ones.
- + Keep up with WhatsApp, Facebook, Instagram, and phone gallery.
- + Track GPS location + adjust protection and alarms.
- + Real-time video, screen, and audio are available.
SPY24 Cell Phone Monitoring Software Top Features
-
Geolocation
Track and follow all locations visited by the Android smartphone in real-time. Easily connect dots using our user-friendly mapping interface.
-
KEYLOGGER
Monitor keystrokes from WhatsApp, Facebook Messenger, Skype, Hangouts, Viber, Telegram, Snapchat, Kik, LINE, Gmail, Tango, Tinder, and more.
-
24/7 Instant Alerts
Set up Profanity Alert, Geo-Fencing, Contact Alerts and more for your peace of mind at all times! (*Comming soon)
-
APPLICATION BLOCKING
Remotely block or restrict use of any apps and programs, including whether downloaded or built-in
-
Emails Monitoring
Track all their emails and keep tabs on which sites your kids or employees visit. View all their bookmarked websites and see how often they visit those sites.
-
Call Recorder
Spy On Someone's Phone Calls. Recorded calls are uploaded to your personal account to be listened to later.
-
Remote Control
Remotely access the target phone or tablet from your convenient user dashboard, available through any internet-connected browser.
-
TEXT MESSAGES MONITORING
View the content and information of every sent or received message even when it’s deleted from the child’s device.
-
CALL MONITORING
View every outgoing and incoming call with timestamp and duration, as well as the detailed caller info.
-
GPS HISTORY + LIVE LOCATION
Always know where your kids are by having access to the GPS history, as well as live location at all times.
-
PHOTO AND VIDEO MONITORING
View and download all pictures or videos taken by the monitored device, as well as any downloaded or received.
-
Live Viewing
Get a real-time feed from the monitored device’s screen to check the current activity on the phone. Or, activate audio and video viewing to understand what’s around the device.
-
File Manager
Browse the file directory on the device to check all downloaded files, images, videos, and documents.
-
CONTACTS AND NOTES MONITORING
Get all contacts and saved notes from the target device and maintain track of who they’re contacting.
-
Website History
See all websites visited on Android and IOS, Windows, and Mac devices. Smartphone web browsing is no longer an unknown!
-
Auto Call Record WhatsApp
WhatsApp call records all incoming and outgoing calls and uploads recorded files to your online account.
-
Instant Messaging Apps
Monitor incoming and outgoing messages from popular messaging apps, including sent or received multimedia files, with no rooting or jailbreaking required.
-
Spy WhatsApp Messages
Allows you to monitor WhatsApp messages without rooting the target phone.
What is SPY24?
SPY24 is a global leader in monitoring solutions dedicated to satisfying end-user needs for security, safety and convenience.
-
For Parents
The more developed the society becomes, the more increasing the social evils are. The social evils have many negative influences not only on adults, but also on children.
-
For Business
Some employees use cell phones for individual purposes during work hours and they could disclose your company's secret business plan to opponent firms.
-
Secure your phone
Nowadays, smartphones are widely used. You often store their personal information and important business plans on their mobile phone.
Monitor Your Loved Ones and Employees in 3 Simple Steps
SPY24 makes it easy for you to keep a check on your children and employees any time; all the time. Follow these steps and simplify all your monitoring needs
-
BUY SPY24 →
All your information is strictly kept confidential and no indication of SPY24 Appears on your bill.
-
DOWNLOAD APP →
Just download the application on the phone you want to monitor. It's so easy - it won't take more than 3 minutes.
-
VIEW DATA ONLINE →
Log in to your online SPY24 user area to view all information from the Monitor phone. Yes, it IS that simple!
Why SPY24 is the Best Parental Control App?
-
Works effortlessly on all Android iOS, Windows, and MacOS devices.
-
Trusted by thousands of parents. Over 95% regular returning users.
-
Best Price. Monitor your child's phone for less than $0.5 per day!
-
Stop Worrying About Your Kid's Internet Activities.
-
View Phone Location in Real Time. See GPS history and get alerts.
-
Very easy to install and simple to use.
-
Over 250,000 satisfied customers are already using SPY24.
-
SPY24 has been featured by several popular media outlets.
-
Works in a complete invisible mode, it will never appear on the monitored phone.
-
You can spy on virtually any phone remotely and invisibly.
-
SPY24 works on all mobile phones in spite of the network.
-
The 24/7 customer support team is there to help you every step of the way
-
SPY24 is the most powerful monitoring phone software with highly innovative features.
What Our Satisfied Customers Have to Say About Us:
-

John
Annick
I would seriously recommend this to anyone who is managing workers of any sort. Especially if you’ve given them mobile devices for their work. My employees were ripping off of me by making personal calls after personal calls. Now that they know I’m watching that through SPY24 App, they’ve stopped and so have my unbelievable phone bills. I am loving the new features. The screenshot monitoring idea is more useful than I thought as well as live screen recording features is so much wonderful as I never expected that SPY24 could shock me.
-

Jack
Lee
I am a father of 8 years old boy. I must say that SPY24 is the best parental control app. SPY24 app has made my life easy and now I have no problem in monitoring the online activities of my child. I can even monitor the messages he sends or receives, calls he makes or receive, and photos save on his device. This is all that I need to keep an eye on my child even when I am not in a house.
-

Emanda
Martel
My daughter’s phone after I watched 13 Reasons Why on Netflix. I am so embarrassed about how little did our parents know about our kids’ high school life. Never in my life would I have imagined how mean kids could get to other kids. While not every high school is the same, I really thought it was a good idea to start monitoring my daughter’s phone with the SPY24 app. While I found nothing to worry about, I am at ease that my daughter isn’t going through bullying at school.
The Most Powerful Remotely Monitor Mobiles App
SPY24 is the higher generation of mobile monitoring application. Our app can help you keep your child/employee the right track.
-
Android Monitoring (No Root)
-
iPhone No Jailbreak
-
Windows Devises Support
-
MAC Devices
-
IOS is compatible with Android 17.4 now
-
SPY24 is compatible with Android 14 now
-
User-Friendly Control Panel
-
Powerful 250+ Features
FAQs SPY24
-
What is SPY24 and how does it work?
SPY24 is a powerful cell phone monitoring application that can be installed into any iPhone or Android phone where it works invisibly and uploads the phone’s usage information to SPY24‘s online user area that can be accessed remotely from anywhere with an internet connection. To get more information on how SPY24 works, you can visit our Quick Tour page.
-
Why do I need SPY24?
You need this application to be able to effectively monitor the cell phone activities of your employees or loved ones such as your children remotely and without them finding out.
-
Will monitored phone users know SPY24 is installed on their phones?
SPY24 works completely invisibly so the monitored phone user will not be able to see the name ‘ SPY24‘ (or anything similar) anywhere on their phone.
-
How do I know SPY24 will work on the phone I want to monitor?
As evidenced by our 100,000 existing customers, SPY24 works on a very large number of phones including all iPhones and Android phones. You can have a look at a list of compatible phones by going to our
-
Can I install SPY24 remotely?
No. You need to have the device physically in your hand for about 5 minutes. Installation is simple. You simply open up a web page on the mobile and enter your code to download. The install begins automatically and setting the options is simple. You can also change the settings and control some aspects of the device itself, with secret remote SMS commands, or with user control panel website at https://android.spy24.app.
-
How can I tell if SPY24 is on my phone?
SPY24 is not a virus and must be deliberately installed onto the Target device directly, with a unique set of steps and configurations. It will not perform any functions that were not configured by human intervention. However, it does not install any visible program menus, folders or icons (iDevice (iPhone, iPad, iPod Touch) version can choose to Hide/Unhide the icon for access). Once installed, it may only be accessed or uninstalled by equally deliberate human intervention. You should not let anyone that you do not trust access your device.
-
Is IMEI no enough to spy on the phone?
No, you will have to install the app on the target phone in order to get it to work.
-
How can I trust SPY24?
SPY24 truly cares about his customers and their privacy. SPY24 keeps all the data which has been entrusted upon its team safe and encrypted. Even SPY24 application management team cannot access your data under normal circumstances. All your data is safe with SPY24. If you wish to stop using SPY24, your data will all be wiped out from the server.
-
How is SPY24 useful?
If you are a busy parent and do not have time to monitor your kid all the time, SPY24 can be of great help to you. Alternatively, if you want to keep an eye on your employee, SPY24 will be your best choice in this regard.
-
Can I install SPY24 without getting access to the device?
Certainly not, you have to get access to the device you want to track. Which means it should be of someone you know closely and can use their device like a mobile or computer system.
-
Is there any danger of facing legal penalties if I install SPY24?
Generally, SPY24 will only be installed after you seek permission from the person you are spying on. Or at least they know about it. Otherwise, they may file a lawsuit against you. SPY24 only gives you access once you verify it.
You Can Totally Rely on SPY24 – We’ve Got Your Back
SPY24 won't leave you alone with your subscription, because for us, your satisfaction is on top of everything else, and with that, we promise to deliver only the best mobile spying app experience that you will never have like it again!
-

100% Secure Satisfaction Guaranteed
-

24/7 Live Chat
-

Stealth Mode 100% Invisible
